 1
1 1
1
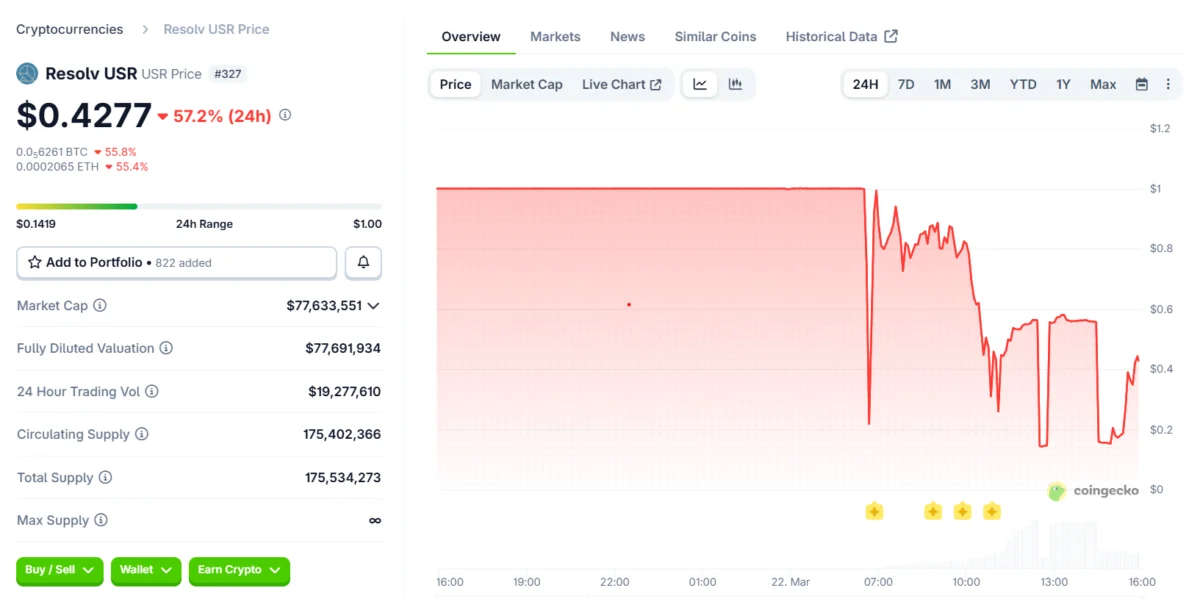
Resolv Labs issued a statement on Sunday aimed at reassuring its user base following a significant exploit that targeted the issuance mechanics of its USR stablecoin. The attack led to the token de-pegging from its intended dollar value, prompting a swift response from decentralized finance (DeFi) protocols with exposure to USR to mitigate potential fallout.
Earlier on Sunday, reports emerged detailing how an attacker exploited vulnerabilities in USR’s minting process. This exploit allowed for the creation of tens of millions of unbacked USR tokens, which were subsequently dumped onto DeFi liquidity pools. The sudden influx of supply overwhelmed the market, causing the stablecoin to break its $1 peg. Resolv Labs, in response, was forced to pause protocol functions to assess the extent of the damage.
According to data from CoinGecko, the USR token experienced a dramatic price drop, falling as low as $0.14, an 86% decrease from its intended peg. At the time of reporting, the token had seen a partial recovery, trading at $0.42.
In an official statement shared on X (formerly Twitter), the Resolv team affirmed that the protocol’s collateral pool "remains fully intact." They indicated that the issue appeared to be "isolated to USR issuance mechanics." Containment efforts and a comprehensive impact assessment were reported as ongoing.
On-chain data, analyzed by Arkham and corroborated by the Web3 security firm Cyvers, revealed that the attacker had converted the majority of the illicitly minted USR into Ether (ETH). Approximately 11,400 ETH, valued at around $24 million, was realized from selling a portion of the stolen tokens. Independent analysts also observed that the remaining 36.74 million USR tokens were "still being continuously dumped."
Michael Pearl, vice president of Go-To-Market and strategy at Cyvers, explained to Cointelegraph that the rapid inflation of USR supply, exceeding the market’s absorption capacity, led to the immediate de-pegging. This significantly impaired the value of the remaining tokens.
The exploit triggered a rapid response from decentralized finance (DeFi) protocols that held exposure to Resolv. Liquid staking provider Lido confirmed that user funds within Lido Earn were secure. Merlin Egalite, co-founder of Morpho, emphasized that the lending protocol’s core contracts were unaffected, with exposure limited to specific vaults. Stani Kulechov, founder of Aave, stated that the Aave platform had no direct exposure to USR and that Resolv was in the process of repaying its outstanding debt.

The X account "yieldsandmore" highlighted potential losses within Resolv’s junior RLP tranche, pointing to possible knock-on effects for yield platforms like Stream and yoUSD that utilized RLP as collateral.
Pearl further elaborated that, based on available data, the exposure appeared to be "relatively concentrated" within lending markets and leverage loops, rather than representing a system-wide risk. The primary impact was observed in protocols that integrated USR, wstUSR, or RLP into their lending, leverage, or yield generation strategies.
He noted that several protocols, including Euler, Venus, Lista, and Fluid, had proactively implemented precautionary measures such as pausing markets or isolating vaults. Other protocols declared no exposure whatsoever. "It is more accurate to describe the risk as concentrated with localized spillover, rather than widespread contagion," Pearl stated.
Charles Guillemet, Chief Technical Officer at Ledger, also weighed in on X, assessing the fallout and concluding that, due to the relatively smaller market capitalization of USR, "this is not a Terra Luna-type event."
The incident has also raised questions regarding the limitations of smart contract security audits. Resolv’s smart contracts have undergone multiple audits since the beginning of 2024. However, Pearl cautioned that while audits are "necessary," they are also "inherently static and scoped." He argued for the necessity of real-time, artificial intelligence-powered monitoring to "continuously analyze protocol activity" and detect anomalies as they emerge.
For stablecoin systems, this continuous monitoring should involve real-time tracking of mint and burn flows against expected behavior, constant validation of supply against reserves and backing assets, and the detection of anomalies in oracle inputs, pricing, and liquidity conditions.
The security firm Pashov, which audited Resolv’s staking module in July 2025, characterized Resolv’s design as "good." They identified the root cause of the exploit not as a design flaw, but rather as a "private key compromise," likely stemming from an operational security lapse. "We have to understand how that happens," a representative from Pashov stated.
Cointelegraph reached out to Resolv Labs for comment but had not received a response by the time of publication.