 1
1 1
1
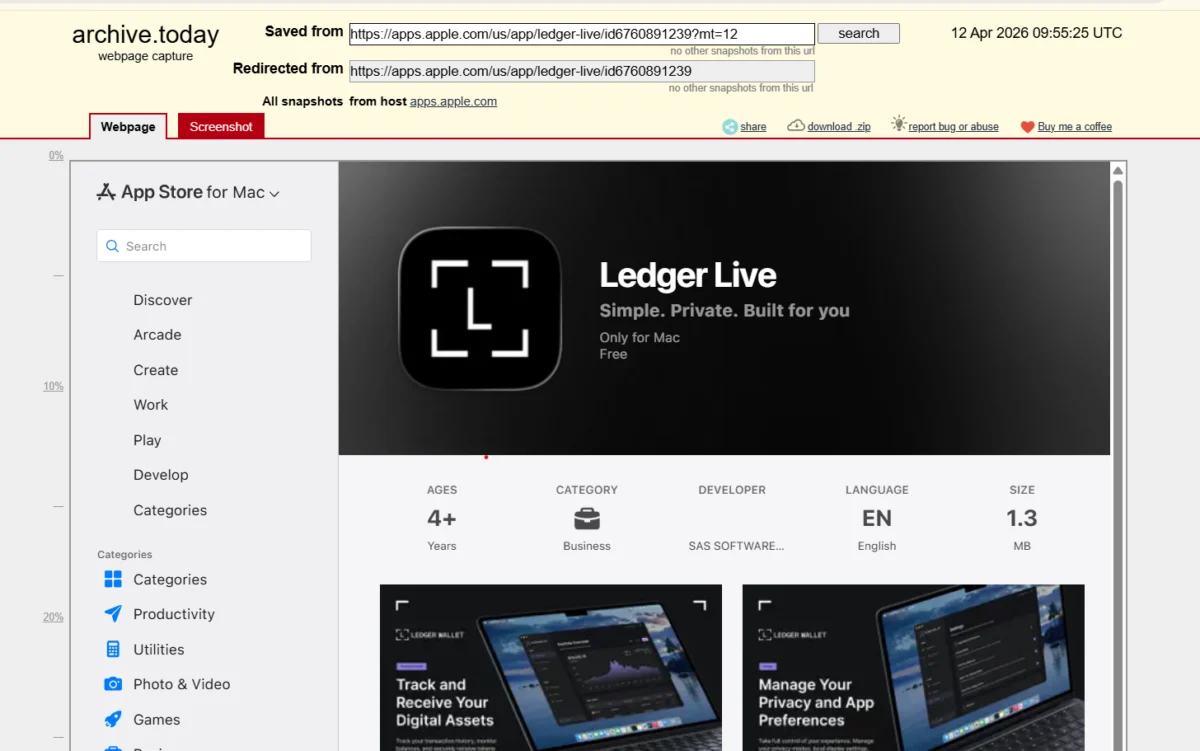
Onchain investigator ZachXBT has revealed a sophisticated phishing scam involving a fake Ledger Live application that was listed on Apple’s App Store. This malicious app is believed to be responsible for the theft of approximately $9.5 million in cryptocurrency from over 50 suspected victims between April 7 and April 13. The findings were detailed in a Telegram post by ZachXBT on Tuesday.
The alleged thefts impacted users across a wide range of blockchain networks, including Bitcoin, Solana, Tron, XRP Ledger, and Ethereum Virtual Machine (EVM)-compatible networks. ZachXBT’s investigation indicates that the stolen funds were subsequently laundered through more than 150 KuCoin deposit addresses. These addresses are reportedly linked to a centralized mixing service known as AudiA6.
Apple removed the fraudulent app from its App Store on April 13. ZachXBT’s report highlighted three significant individual losses, each exceeding seven figures. One victim reportedly lost around $1.95 million in a combination of Bitcoin (BTC), staked Ether (stETH), and Ether (ETH). Another victim suffered a loss of $3.23 million in USDT on April 9, while a third individual lost approximately $2 million in USDC on April 11.
In addition to detailing the scale of the theft, ZachXBT also pointed to broader concerns regarding the cryptocurrency exchange KuCoin. The investigator noted an observed increase in illicit activity associated with KuCoin recently. This comes after KuCoin faced a ban on onboarding new European Union users in February, shortly after obtaining its Markets in Crypto Assets Regulation (MiCA) license. ZachXBT also raised questions about whether this incident might provide grounds for a class-action lawsuit against Apple.
The key details surrounding the total losses, the number of victims, and the specific laundering route are based on ZachXBT’s independent findings. As of the time of publication, neither Apple nor KuCoin had officially confirmed these details. Cointelegraph reached out to both companies for comment but had not received a response.
Ledger’s Security Advisory: Never Enter Seed Phrases into Apps
In response to the ongoing threat, Charles Guillemet, Chief Technology Officer at Ledger, issued a statement to Cointelegraph emphasizing the critical importance of protecting recovery phrases. He reiterated Ledger’s long-standing policy: the company never requests users to provide their 24-word recovery phrase. Guillemet strongly warned users against treating any software environment, including app stores, browsers, or desktop applications, as inherently secure.

"You cannot trust the software environment around you – not your browser, not your app store, not your desktop," Guillemet stated. He further explained that malicious actors actively seek out opportunities wherever they exist, including official distribution platforms. This underscores the vulnerability that can arise even from seemingly legitimate sources.
This latest incident is not an isolated event. A similar, albeit smaller, case was reported on Monday involving musician Garrett Dutton, professionally known as "G. Love." Dutton disclosed that he lost approximately $420,000 in Bitcoin after downloading an application that impersonated Ledger Live from the Apple App Store and subsequently entered his seed phrase. ZachXBT also linked the stolen assets in this case to KuCoin deposit addresses.
The modus operandi of these scams involves creating convincing fake applications that mimic legitimate cryptocurrency wallet software. Users, often unaware of the deception, download these apps, believing them to be official. The critical error occurs when victims are prompted to enter their private recovery or seed phrases into these fraudulent applications, granting the attackers direct access to their digital assets.
The incident highlights a persistent challenge in the cybersecurity landscape: the difficulty of distinguishing between legitimate and malicious applications, even within curated digital marketplaces. While app stores implement review processes, sophisticated scams can sometimes bypass these safeguards. The involvement of a centralized mixing service like AudiA6 further complicates the tracing and recovery of stolen funds, as it obscures the trail of illicit transactions.
The reliance on centralized exchanges like KuCoin for laundering, as alleged in this case, also raises questions about the effectiveness of their Know Your Customer (KYC) and Anti-Money Laundering (AML) procedures. While exchanges are increasingly under regulatory scrutiny, the continuous emergence of such schemes suggests that vulnerabilities remain.
The advice from Ledger and security experts like ZachXBT remains paramount: extreme caution and vigilance are necessary when managing cryptocurrency assets. Users are consistently reminded to download software only from official sources, verify the authenticity of applications, and, most importantly, never share their private keys or seed phrases with any application or third party, regardless of how legitimate it may appear. The security of digital assets ultimately rests on the user’s ability to safeguard their sensitive recovery information.
The ongoing investigation by ZachXBT aims to shed further light on the individuals and networks behind this elaborate phishing operation. The involvement of multiple blockchain networks and the use of a mixing service indicate a well-resourced and organized criminal enterprise. The incident serves as a stark reminder of the evolving threats in the cryptocurrency space and the critical need for robust security practices among users and vigilant oversight from platform providers.