 1
1 1
1
In a significant cybersecurity incident underscoring the escalating risks of supply chain attacks, hackers have reportedly infiltrated Anodot, a prominent business monitoring software maker, subsequently stealing sensitive data from at least a dozen of its corporate clients. The breach has left these companies vulnerable to severe extortion demands and the potential public release of their proprietary information, highlighting a critical vulnerability in the interconnected digital ecosystem.
The sophisticated cyberattack, attributed to the notorious ShinyHunters hacking group, saw the perpetrators leveraging Anodot’s compromised systems to gain unauthorized access to its customers’ cloud-stored data. Both Bleeping Computer, which was among the first outlets to break the news of the Anodot breach, and BBC News have reported that ShinyHunters is actively threatening to publish the stolen data unless their ransom demands are met, intensifying the pressure on affected organizations.
This incident serves as a stark reminder of a growing trend where cybercriminals target software providers, particularly those offering business-critical tools, as a strategic gateway to compromise multiple downstream companies in a single operation. Such "supply chain" attacks exploit the trusted relationships between vendors and their clients, making them incredibly potent and difficult to defend against.
Anodot, a company specializing in AI-powered analytics for detecting outages, anomalies, and other operational issues that could impact revenue, confirmed the commencement of the incident on April 4. According to a statement posted on its official status page, the company’s data connectors experienced a critical failure, disrupting customers’ access to their cloud-hosted data. This disruption was, in fact, a symptom of the deeper compromise. Reports indicate that the ShinyHunters group successfully breached Anodot’s internal infrastructure and exfiltrated authentication tokens. These tokens, crucial for customers to securely access their data residing in various cloud storage environments, were then weaponized by the hackers to illicitly download vast quantities of customer data from these cloud repositories.
The ripple effect of the breach quickly extended to major cloud storage providers. Snowflake, a widely used cloud data warehousing company, was compelled to sever the connection between Anodot customers and their data stores after detecting "unusual activity" within certain accounts. This proactive measure by Snowflake underscored the severity of the unauthorized access and the immediate threat to data integrity and confidentiality.
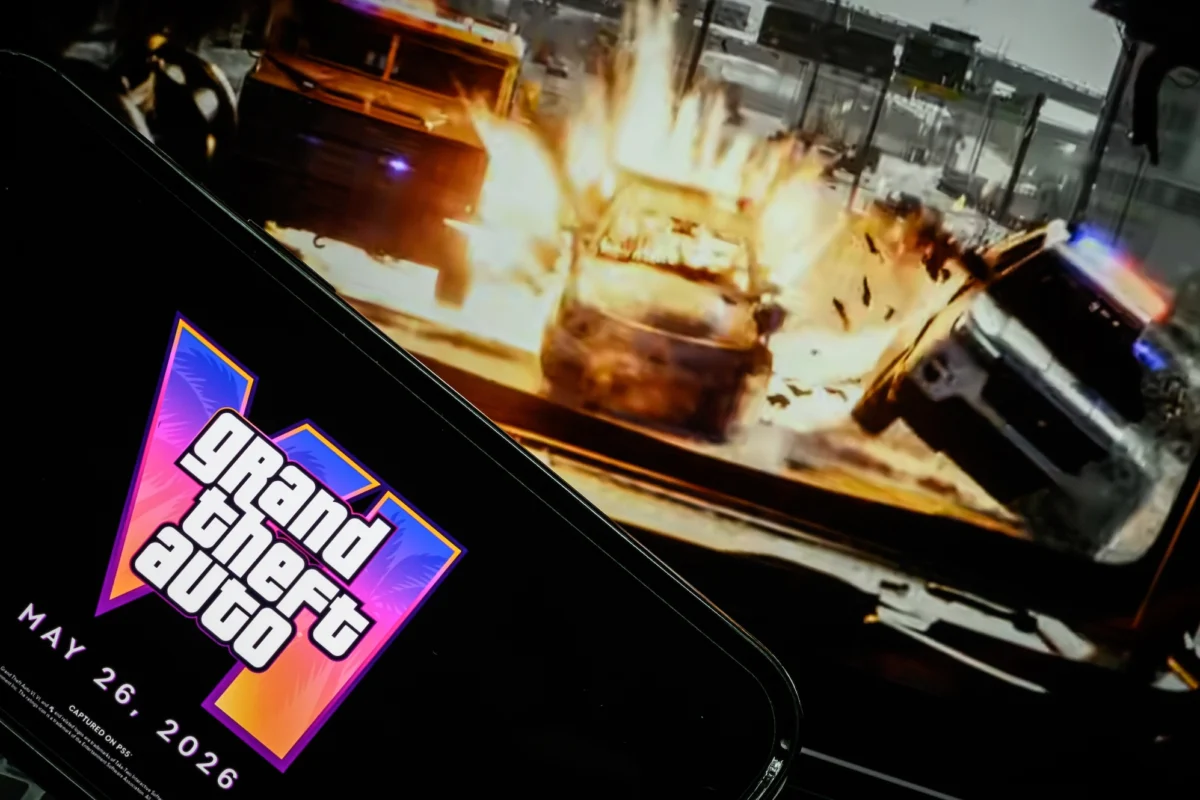
Among the high-profile companies reportedly impacted by the breach is Rockstar Games, the acclaimed developer behind iconic video game franchises such as Grand Theft Auto and Max Payne. Gaming news outlet Kotaku was among the first to report Rockstar Games’ potential involvement. In response to inquiries, Rockstar spokesperson Murphy Siegel issued a statement to TechCrunch, confirming that "a limited amount of non-material company information was accessed in connection with a third-party data breach." Siegel further asserted that "This incident has no impact on our organization or our players," attempting to downplay the significance of the compromise.
However, this is not the first time Rockstar Games has found itself in the crosshairs of cybercriminals. In 2022, the company suffered another major breach where hackers stole and subsequently published an early development trailer for its highly anticipated flagship title, Grand Theft Auto VI. This repeated targeting, whether directly or indirectly through third-party vendors, highlights the persistent threat faced by prominent entertainment companies and the value of their intellectual property to malicious actors.
As of Monday, both Snowflake and Glassbox, the parent company of Anodot, had not responded to TechCrunch’s requests for comment, leaving many questions about the extent of the breach and the ongoing mitigation efforts unanswered. This silence, while sometimes standard procedure during active investigations, often adds to public and stakeholder concern regarding transparency and accountability.
The ShinyHunters group, primarily composed of English-speaking hackers, has established a notorious reputation for their sophisticated data theft and extortion schemes. Their operational tactics frequently involve advanced social engineering, a psychological manipulation technique used to trick individuals into divulging confidential information or granting access to secure systems. The group is particularly adept at impersonating IT help desk personnel or support staff, exploiting human vulnerabilities to gain initial footholds within large corporate networks. This method allows them to bypass technical security controls by manipulating employees into unknowingly facilitating access to accounts or systems.
ShinyHunters strategically targets companies that manage and store substantial volumes of data in cloud environments, recognizing these repositories as lucrative targets for mass data exfiltration. Over the past year, the group has demonstrably focused its attention on Software-as-a-Service (SaaS) providers and data integrators like Anodot, as well as others such as Gainsight and Salesloft. These companies provide platforms that enable their customers to access, analyze, and manage large datasets in their cloud storage. By compromising these integrators, ShinyHunters aims to steal not just customer data, but also critical authentication credentials, including passwords and, most importantly, tokens. In several documented cases, the tokens stolen from one compromised entity have subsequently been used to breach additional companies, demonstrating a dangerous domino effect inherent in these supply chain attacks.
The modus operandi of ShinyHunters, involving the theft of data followed by extortion attempts, places significant pressure on victim organizations. The threat of public data release can inflict severe reputational damage, expose sensitive corporate secrets, and trigger regulatory penalties, making the ransom demands a difficult dilemma for affected companies. The group’s preference for cloud-based targets underscores the ongoing shift in enterprise IT infrastructure and the corresponding need for enhanced security measures in cloud environments. Organizations are increasingly reliant on third-party SaaS applications for critical business functions, making the security posture of these vendors paramount. A breach at one vendor can rapidly propagate across an entire client ecosystem, creating a complex web of compromised entities.
The incident at Anodot serves as a critical case study in the evolving landscape of cyber threats, emphasizing the imperative for companies to implement robust third-party risk management frameworks. This includes rigorous vetting of vendors, continuous monitoring of their security practices, and establishing clear protocols for incident response and data protection. Furthermore, organizations must prioritize the security of authentication tokens and credentials, implementing multi-factor authentication (MFA) and least privilege access principles across all systems and services, especially those connecting to external cloud platforms. The ongoing battle against sophisticated cybercriminal groups like ShinyHunters necessitates a multi-layered defense strategy, combining advanced technological safeguards with continuous employee training and a strong culture of cybersecurity awareness to protect against both technical vulnerabilities and human error.
Zack Whittaker, the security editor at TechCrunch and author of the weekly cybersecurity newsletter, "this week in security," continues to report on these critical developments. He can be reached for encrypted messages at zackwhittaker.1337 on Signal, or via email at [email protected] for inquiries or to verify outreach.