 1
1 1
1
The Federal Bureau of Investigation (FBI), in coordination with the Justice Department, has seized and taken down two websites linked to the pro-Iranian hacktivist group known as Handala. This action comes just a week after the group publicly claimed responsibility for a destructive cyberattack targeting the U.S. medical technology giant, Stryker. The takedown represents a significant move by U.S. law enforcement to disrupt the digital infrastructure of groups believed to be operating on behalf of, or in coordination with, foreign state actors.
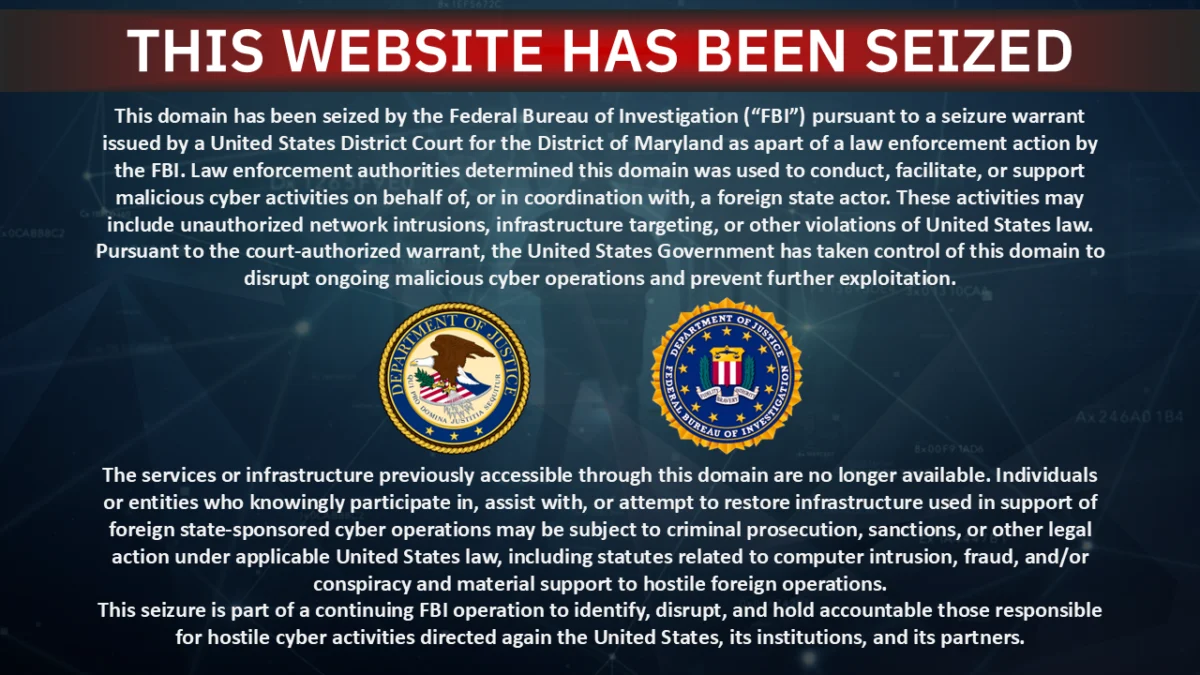
As of Thursday, the digital landscape where Handala once operated its online campaigns was dramatically altered. One of the seized websites served as the primary platform for the group to publicize its cyberattacks and propaganda. The second website was notably used for doxing, a malicious practice involving the publication of private identifying information about individuals. Handala specifically targeted dozens of people, alleging ties to the Israeli military and prominent defense contractors such as Elbit Systems and NSO Group. Both websites now display a prominent banner announcing the law enforcement action, signaling the U.S. government’s assertion of control over these domains.
While the official seizure announcement did not provide a detailed explanation for the precise legal grounds behind the takedowns, the language used strongly suggested that U.S. authorities believe these sites were operated by hackers with direct links to a foreign government. The banner declared, "Law enforcement authorities determined this domain was used to conduct, facilitate, or support malicious cyber activities on behalf of, or in coordination with, a foreign state actor." It further elaborated on the government’s intent: "The United States Government has taken control of this domain to disrupt ongoing malicious cyber operations and prevent further exploitation." This statement underscores the U.S. government’s posture against state-sponsored cyber threats and its commitment to proactive measures to safeguard national security and critical infrastructure.
TechCrunch, the publication reporting on the incident, independently verified the website seizures. Their investigation involved examining the nameserver records associated with the domains, which confirmed that these records now point to servers directly controlled by the FBI. This technical confirmation provides concrete evidence of the U.S. government’s successful intervention. When approached for comment, both the FBI and the Justice Department did not immediately respond to TechCrunch’s inquiries, maintaining a characteristic silence on ongoing operations.
The seizure notice itself, prominently displayed on the now-defunct websites, served as a stark visual representation of the law enforcement action. The image of this notice, depicting the FBI and U.S. Department of Justice logos alongside the declaration of seizure, quickly circulated as a symbol of the digital confrontation between state actors and hacktivist groups.
In a series of rapid-fire announcements posted on its official Telegram channel on Thursday, Handala swiftly acknowledged the takedown of its websites. The group vehemently denounced the seizures, characterizing them as "a desperate attempt to silence our voice." In its defiant statements, Handala framed the actions as "an act of digital aggression" that, according to the group, only served to "highlight the fear and anxiety our actions have instilled in the hearts of those who oppress and deceive." The hacktivists further asserted that "although they attempt to erase the evidence and hide their crimes through censorship and intimidation, their actions only confirm the impact of our mission. The pursuit of justice cannot be stopped by taking down a website, the movement for truth will persist and grow stronger." This rhetoric is typical of hacktivist groups, aiming to galvanize supporters and project an image of resilience in the face of state-level countermeasures. Adding to Handala’s operational challenges, the group’s official X (formerly Twitter) account had also been recently suspended, further curtailing its public outreach capabilities. A message sent to Handala’s official chat account remained unanswered, indicating either a disruption in their communication channels or a strategic silence following the takedowns.
Handala’s activities have been documented since at least the October 7, 2023, attacks by Hamas, a pivotal moment that significantly escalated tensions in the Middle East and triggered a surge in cyber operations linked to the conflict. The group is widely believed to maintain ties with the Iranian regime, positioning it within the broader landscape of state-backed cyber proxies that Iran is known to employ.
Last week, Handala drew international attention by claiming responsibility for a significant cyberattack against Stryker, a major U.S. medical technology company employing over 56,000 individuals across dozens of countries. The hacktivists stated that the attack was executed in retaliation for a purported U.S. government missile strike that they claimed hit an Iranian school, resulting in the deaths of at least 175 people, many of whom were children. While the U.S. government has not publicly acknowledged such a strike, Handala’s assertion highlights the politically charged motivations often underpinning such cyber operations. The choice of Stryker as a target was likely influenced by its significant contracts with the U.S. government; last year, the company secured a substantial $450 million contract to supply medical devices to the Department of Defense, making it a valuable target for groups seeking to disrupt U.S. interests or inflict economic and reputational damage.
The technical details of the Stryker attack, as claimed by Handala, paint a concerning picture of sophisticated intrusion and destructive intent. The group reportedly breached an internal Stryker administrator account, a highly privileged access point that typically grants extensive control over a company’s IT infrastructure. This compromise allegedly provided Handala with "near-unlimited access" to Stryker’s Windows network. From there, the hackers claimed to have taken control of the company’s Intune dashboards. Microsoft Intune is a widely used cloud-based service that enables organizations to manage employee laptops, mobile devices, and applications remotely. Access to Intune dashboards provides powerful capabilities, including the ability to configure, deploy, and critically, wipe data from managed devices. With this level of control, Handala allegedly proceeded to wipe devices owned by both the company and its employees, causing significant operational disruption and data loss.
As of Tuesday, Stryker confirmed that it was still in the process of restoring its computers and internal network systems in the aftermath of the devastating cyberattack. The prolonged recovery period underscores the severity and impact of the destructive actions carried out by Handala, highlighting the challenges companies face in rebuilding their digital infrastructure after such breaches.
Nariman Gharib, a U.K.-based Iranian activist and independent cyber-espionage investigator, offered insights into the implications of the takedowns. Gharib expressed that the seizures represent "good news" in the fight against such groups. He emphasized the immediate impact, stating, "Their organizational and management structure is currently disrupted, and at any moment, members of this group may be targeted by missile strikes, just like other cyber forces of the regime." This assessment points to the potential for further physical or digital targeting of individuals associated with the group, illustrating the high stakes involved in state-sponsored cyber warfare. However, Gharib also cautioned against underestimating the resilience of such actors. He noted, "But this does not mean that their activities may stop — no. It is possible that future leaks may be published by this group through media close to the IRGC," referring to Iran’s Islamic Revolutionary Guard Corps. This suggests that while the immediate digital infrastructure of Handala has been disrupted, the underlying capabilities and intentions of the group, and potentially its state sponsors, remain intact, and they may simply adapt their methods of operation and communication to circumvent future takedowns. The ongoing cat-and-mouse game between law enforcement and state-linked hacktivists continues to evolve, with digital infrastructure takedowns serving as one tool in a multifaceted strategy to counter persistent cyber threats.