 1
1 1
1
 1
1 2
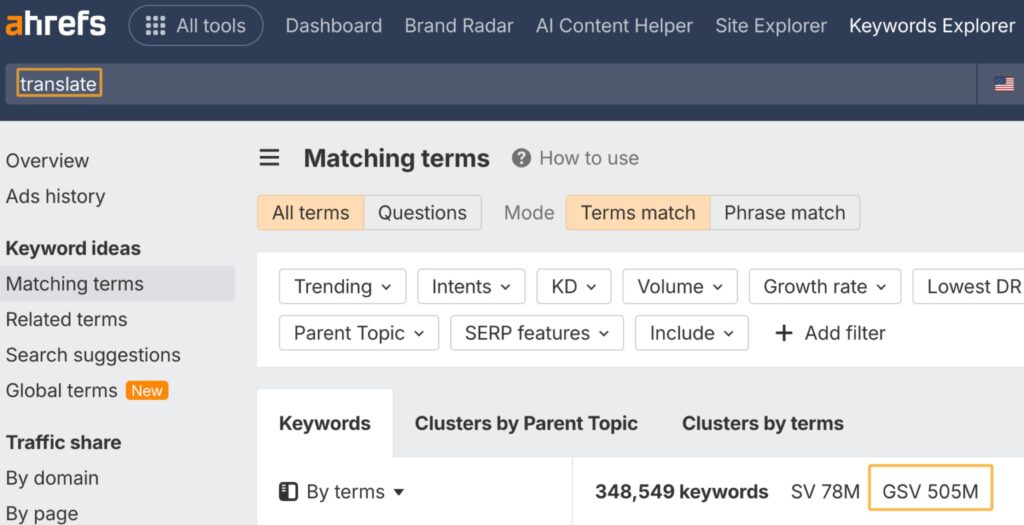
2 3
3
In contemporary US history, a significant number of Americans find themselves in profound opposition to the actions of the federal government, often with little expectation of a political resolution emerging from traditional top-down channels. This widespread disillusionment has propelled millions to seek alternative avenues for change, turning to a bottom-up approach to resistance: grassroots organizing. However, as citizens mobilize to establish movements dedicated to safeguarding immigrants, confronting the aggressive incursions of the Department of Homeland Security (DHS) and its agencies into urban centers, and advocating for fundamental civil rights and policy reforms, they confront an formidable adversary. This adversary is a federal government armed with expansive surveillance capabilities and bolstered by the extensive cooperation of Silicon Valley technology companies that possess vast repositories of Americans’ personal data.
This challenging environment transforms political, social, and economic organizing into a high-stakes dilemma. The core question becomes: How can individuals of diverse ages, backgrounds, and technical proficiencies be brought together into a cohesive mass movement without simultaneously exposing them to the intense monitoring and targeted actions of government entities? This concern is particularly acute when considering agencies like Immigration and Customs Enforcement (ICE) and Customs and Border Protection (CBP). These agencies are known for their paramilitary ambitions, a documented tendency to operate outside legal boundaries, and budgets that, in some instances, surpass the military expenditures of entire nations.
Organizing effectively and securely in an era defined by pervasive surveillance demands a multifaceted approach. It necessitates not only a strong grasp of technical security principles but also a delicate balance between maintaining secrecy and fostering openness, according to Eva Galperin, the director of cybersecurity at the Electronic Frontier Foundation (EFF), a prominent nonprofit dedicated to digital civil liberties. "You may want to limit access to some information to a smaller group of people, and you need to consider the platforms you are using, so that when law enforcement shows up to Google with a subpoena, there’s nothing sensitive it can hand over," Galperin explains. She quickly adds, however, that this cautious approach must be weighed against a fundamental truth of activism: "the majority of organizing is done in public, with other people, because the power of organizing is in numbers and solidarity."
Given this complex predicament, there is no single, simple set of technological tips that can universally guarantee the safety of organizers striving to build a movement. Instead, a combination of thoughtful approaches, practical guidelines, and specific tools can significantly enhance security. To provide comprehensive guidance on how to organize and collaborate effectively in a surveillance state, WIRED consulted a diverse group of experts, including technologists, experienced activists, humanitarian aid groups, and leading cybersecurity specialists. Their collective insights form the basis of the recommendations presented here.
The foundational step towards more secure and surveillance-resistant organizing is a process that digital security experts and seasoned organizers refer to as "threat modeling." This involves systematically envisioning potential adversaries—who they are, what their objectives might be, and what specific information they might seek to surveil or exploit. By engaging in this exercise, organizers can establish clear distinctions between information that can be publicly shared or discussed on less private platforms, and those critical aspects of their organizing efforts that absolutely must remain confidential. In virtually all cases, a blend of both approaches will be essential.
Matt Mitchell, a former founder and security trainer at CryptoHarlem and currently the CEO of the risk-mitigation firm Safety Sync Group, cautions against an overly rigid approach to security. "If you have no rules on what should or should not be encrypted or secured, then you’re going to want to encrypt every single thing," Mitchell observes. While this impulse "comes from a good place," he warns, "that creates a lot of barriers and makes it more likely that someone will make mistakes." An excessive focus on secrecy can inadvertently hinder accessibility and operational efficiency.
EFF’s Galperin suggests a practical guideline: consider what information is inherently destined to become public anyway, and when. For instance, the exact time and location of a small, internal planning meeting might warrant strict secrecy. However, if an event is soon to be public—such as the organization of a large-scale rally that requires permits from city officials—the pressure to secure every detail of its planning decreases significantly. Galperin also stresses that an atmosphere of excessive secrecy can be off-putting to potential new members, thereby undermining the movement’s growth. "A very, very large part of activism is telling people what you’re doing," she emphasizes, characterizing much of this work as "casseroles and phone trees. It is deeply unsexy, but also not secret work."
Taylor Fairbank, cofounder of the humanitarian relief group Distribute Aid, offers a real-world example. He notes that much of his organization’s logistical and communication work—connecting specific supplies with communities in need, for instance—can, and often must, occur openly or on platforms that might be subject to surveillance. "I will never be able to leave Facebook because I have the cutest grandparents in the UK who reach out to me once a year offering a bunch of knitted hats and sweaters to send to a refugee camp in Europe," he explains. "It’s my job to be available and to be on insecure tools to help match those opportunities and translate that across geographical boundaries."
Crucially, however, other categories of information, such as the precise locations of Distribute Aid’s warehouses, are meticulously protected. "We will never post warehouse addresses online, because we have seen our warehouses and our partners’ warehouses get targeted for theft and political violence," Fairbank states, highlighting the tangible risks involved. "I really recommend explicitly identifying sensitive data and holding that close."
This approach means that for every mode of collaboration or communication, organizers must carefully assess whether and how it requires protection. For each element of an organization’s digital footprint deemed truly sensitive, specific measures must be taken: encryption, timed deletion, storage under direct organizational control rather than in the cloud, or a combination of these tactics. The following sections delve into the specific tools and practices recommended by experts. In essence, attempting to keep everything secret is neither practical nor always desirable. Instead, the focus should be on creating a robust threat model, identifying truly sensitive information, and then making a concerted effort to protect it through encryption, secure storage, or timely deletion—while minimizing concern over information that will inevitably become public.
For text and voice communications, the consensus among virtually all activists and security experts interviewed by WIRED points to one primary tool: the encrypted messenger Signal. Its widespread recommendation stems from several critical features. Signal employs end-to-end encryption (E2EE), meaning that only the sender’s and receiver’s devices can decrypt the communications, ensuring that no intermediary—not even Signal itself—can access the content. It is a battle-tested platform, consistently proven reliable in high-stakes environments. Furthermore, Signal is free, open source (allowing independent security audits), highly popular, and sufficiently user-friendly to facilitate the seamless onboarding of new members into an organization. A significant differentiator from alternatives like WhatsApp (which also uses Signal’s encryption protocol for its E2EE messages and calls) is Signal’s commitment to not logging metadata—information such as who is calling or texting whom, and when. This absence of metadata logging is a crucial privacy feature, as metadata itself can often reveal patterns and associations even if message content remains encrypted. Finally, Signal has evolved to become increasingly robust, even supporting group video calls, positioning it as a viable and secure alternative not only to traditional email but also to less secure video conferencing tools like Zoom.
Even with Signal’s inherent strengths, certain practices can dramatically enhance its security posture. Perhaps as important as Signal’s encryption is its disappearing message feature, which allows users to set a timer for messages to automatically delete, ranging from four weeks down to a mere 30 seconds. Turning this feature on is highly recommended. Even a countdown clock of one week for less sensitive conversations can significantly reduce the potential risk of an organization’s communications being leaked or compromised over time. Additionally, organizers should take advantage of Signal’s username feature instead of relying solely on phone numbers when adding new members. This further limits a group’s potential exposure of identifying contact information, as phone numbers are directly linked to real-world identities.
As Signal groups grow in size, however, it’s vital to remember that encryption alone does not provide magical protection against leaks originating from within the group itself—a lesson starkly illustrated by the "SignalGate" scandal during the Trump administration. Galperin advises caution: "If your group has more than 50 people in it, it’s not a private space for communication." To maintain maximum security, truly sensitive information should be confined to the smallest possible groups or communicated directly in one-on-one exchanges.
The effectiveness of end-to-end encryption is also contingent upon the security of the devices at either end of the conversation. All group members should configure authentication to access the Signal app itself; this can be done by navigating to Screen Lock under the Privacy menu in Signal’s settings. For members with access to sensitive data and Signal groups, it is imperative to set up a strong passcode for their devices. Furthermore, consider disabling biometric access (such as face or fingerprint recognition) for that screen lock, and ideally for the phone or computer running Signal entirely. This is because biometric unlocking methods generally offer fewer Fourth Amendment protections against law enforcement searches compared to a strong passcode. The widely reported case of Washington Post reporter Hannah Natanson, where authorities gained access to her linked Signal account via biometric access to her PC despite other phone security measures, serves as a potent reminder of this vulnerability.
If maintaining such a high level of security on a primary device proves too cumbersome for daily use, Galperin suggests a pragmatic solution: dedicate a second device, an "alt phone," specifically for sensitive organizational communications. This device would be configured with heightened security measures. "Compartmentalization is good," Galperin explains, "so that you don’t mix up these two parts of your life—one where you have to be extremely careful and one where you can kind of just live your normal life and do your work." This separation minimizes the risk of inadvertently exposing sensitive data during routine activities.
While various other encrypted communication apps, such as SimpleX, Session, and non-interoperable forks of Signal, have gained traction within the security community, none of the experts consulted by WIRED recommended switching to them. This reluctance is primarily due to their relative lack of extensive testing in real-world scenarios and the significant organizational cost of compelling members to adopt a less familiar, often more complex tool. Experts also strongly cautioned against using private messaging features on social media apps, despite their apparent convenience for organizers, owing to these platforms’ inherent lack of robust privacy guarantees and strong, default encryption.
One communication tool that Signal cannot easily replace, experts conceded, is Slack. Its flexible group messaging and notification features often create a sense of greater efficiency for complex team organizing. However, given that Slack lacks end-to-end encryption, does not offer disappearing message features, and is centrally hosted by a company that cooperates with law enforcement requests, it represents a significant privacy nightmare for organizers. Harlo Holmes, a security trainer and director of digital security at the Freedom of the Press Foundation, points out that even the name "Slack" originally stood for "Searchable Log of all Communications and Knowledge"—a clear indication of its data retention philosophy. "Slack is designed to feel like the water cooler, so you can just say what you want," Holmes notes. "But it’s not your friend." The same warnings apply equally to Discord.
As safer alternatives to Slack, Holmes and other cybersecurity experts recommended tools like Mattermost and Matrix. Both offer enhanced security features: Matrix specifically boasts end-to-end encryption, and both provide options for timed auto-deletion of messages. Crucially, both Mattermost and Matrix can be self-hosted—meaning they can be set up and run on a server owned and controlled by the organization itself, rather than relying on a third-party company like Slack. While self-hosting introduces its own set of significant security challenges, it can still be preferable to entrusting an organization’s entire communication history to a firm that might offer limited resistance or transparency when faced with legal demands from authorities. In summary, use Signal for as many texts, calls, and video chats as possible, and always enable disappearing messages. Remember that encryption is not a panacea; the security of the devices at each end of the conversation, and the level of trust placed in every group member, are equally critical.
Organizing, by its very nature, demands extensive coordination and documentation. Whether it’s a spreadsheet for scheduling community watch shifts or a set of planning documents requiring regular updates from multiple group members, cloud-based tools that offer automatic synchronization, such as the Google Docs Suite or Microsoft Office 365, are often the default choice for most users. However, these platforms inherently place an organization’s sensitive information into the hands of Google or Microsoft, companies that retain the power to revoke access at their discretion or, more critically, to hand over data to any federal agency that presents a legally valid demand.
This presents a difficult decision for organizers: these mainstream tools are undeniably vulnerable to surveillance, yet their widespread recognition and accessibility are often essential attributes when collaborating with individuals from diverse backgrounds and technical aptitudes.
An expensive solution to this quandary exists for well-funded organizations: implementing an enterprise "client-side" encryption scheme. This involves using platforms like Google Docs but managing the encryption keys for their data through a third-party service such as Virtru, thereby preventing Google or the platform provider from accessing the unencrypted content. For grassroots organizers and individuals who cannot afford to spend thousands of dollars annually on such a setup, experts still acknowledge a place for normal, unencrypted Google Docs within most threat models—provided there is a clear understanding and acceptance of the inherent risks.
Evan Greer, the director of the nonprofit advocacy group Fight for the Future, offers a pragmatic perspective: "Will Google hand over your data to the feds if they serve them with a subpoena? Yes. Is it still basically a functional tool for the thing that you’re trying to do? Yeah." She adds a crucial piece of advice for organizations already in motion: "And would I tell you to switch to some cool open-source alternative in the middle of the fight? Not necessarily. We’re in a crisis moment right now. I want organizers out there fighting and organizing, not figuring out how to configure their email." The priority, especially during urgent campaigns, might be continued functionality over ideal security.
The good news is that for situations where prioritizing security in collaboration tools is paramount, and an expensive enterprise setup is out of reach, a growing list of more affordable yet safer options exists compared to mainstream consumer cloud services. The Switzerland-based company Proton offers a comprehensive suite of end-to-end encrypted tools, including its flagship email service Proton Mail, as well as Proton Docs, Sheets, Calendar, and Drive.
(A crucial note regarding Proton Mail: its emails are only end-to-end encrypted when communicating with other Proton Mail accounts. If a Proton Mail user sends an email to a Gmail account, the message is treated like any other on Google’s servers, losing its E2EE protection. For general secure messaging, sticking with Signal, which is designed to only operate with E2EE platforms, is a safer bet as it prevents accidental exposure of communications.)
Free Proton accounts come with 1 GB of storage, and the company provides paid plans at $13 and $20 per month, offering increased storage and additional features like expanded account protection. Proton also caters to larger organizations with business-focused products. (For cloud storage specifically, another Swiss company, Tresorit, offers an end-to-end encrypted option that, while not open source, has been recommended by some experts.)
While offering synchronous collaboration tools with end-to-end encryption is inherently complex, and Proton’s offerings might not be as feature-rich or seamlessly intuitive as traditional web platforms (Safety Sync’s Matt Mitchell points out that its word processor, for example, doesn’t even split documents into pages), the company has focused for years on creating a straightforward and familiar user interface, which significantly aids adoption.
Proton products are open source and undergo independent audits, bolstering their credibility. Maintaining the company’s operations in Switzerland also provides some additional legal protections regarding data privacy due to Switzerland’s robust privacy laws. However, multiple sources informed WIRED that there have been instances where law enforcement compelled Proton to produce metadata about specific customers. A notable case in 2021 involved Proton logging the IP address and device ID of a French activist at the behest of Swiss law enforcement, demonstrating that even strong legal frameworks have limits.
In some respects, a server owned and controlled directly by an organization can be even more secure than one operated by a Swiss company. Fight for the Future’s Greer highlights "self-hosted" options as another robust approach to making an organization’s data more resistant to surveillance. Nextcloud, for example, offers a Google Docs-like collaboration suite that organizations can deploy on their own servers, effectively creating a "private cloud." Another toolset, Cryptpad, provides the same self-hosted option and also end-to-end encrypts data. This combination keeps data out of the hands of untrusted companies while theoretically protecting it even if the organization’s own Cryptpad server is seized or compromised.
However, a major caveat accompanies self-hosting: it is inherently challenging. It demands a dedicated IT professional or team to maintain infrastructure, secure the network, keep software updated, and respond—often in the middle of the night—if a server malfunctions. "People doing activism talk about hosting things locally and think it will be more secure. That depends: How good a systems administrator are you?" asks EFF’s Galperin. "Let me tell you, trying to keep your server up and running and secure is not a part-time job. It is very, very hard to do correctly."
For a well-resourced and sufficiently tech-savvy organization, however, self-hosting can be an extremely powerful option. Fight for the Future, as Greer recounts, has largely "de-Googled" over the past year, transitioning most of its tools to end-to-end encrypted or self-hosted alternatives, including Signal, Nextcloud, Matrix, and the self-hosted wiki tool Outline. (Greer notes that this move was motivated partly by security concerns and partly by a sentiment she describes as "fuck these Big Tech monopolists, we don’t want to use their software if we don’t have to.") Distribute Aid’s Fairbank adds that some nonprofit organizations, such as Movement Infrastructure Research and Rise Against Big Tech, may be able to offer assistance to groups considering self-hosting.
One more risk to consider pertains to web-based services: while they offer the convenience of access from any browser, if the underlying encryption of a secure platform is compromised—for example, by a company legally compelled to undermine its security or whose server is seized—it could expose all browser-based activity within that web tool without any discernible signs of a change to the user. To exercise maximum caution, the most secure way to utilize end-to-end encrypted platforms is through dedicated desktop and mobile applications. In these applications, the software implementing the encryption scheme is downloaded and installed directly, and it can only be altered by installing a new update, offering greater transparency and control. Nextcloud and Cryptpad both provide stand-alone applications, while Proton offers them for services like Mail and Calendar, though not yet for Docs and Sheets.
Beyond the entire spectrum of cloud-hosted collaboration tools, there remains the classic, "old-fashioned" method: keeping copies of files locally on one’s own computer. For collaborating within a small, trusted group on a truly secret document, a simple and secure approach is to take turns editing it offline with a text editor before passing the updated file to the next editor via Signal.
Across all these approaches—from the fully public to the most paranoid—the same fundamental principle applies as in a Signal conversation: a piece of information is only as secure as the least secured device that accesses it. Therefore, as organizers develop their threat model and determine which devices and accounts within their group will have access to their most sensitive data, it is imperative to ensure those endpoints are appropriately locked down. This means implementing full-disk encryption (with detailed guides available for both Windows and Mac operating systems), utilizing strong, unique passwords (a reputable password manager is highly recommended), and enabling multifactor authentication on all accounts, whether they pertain to cloud-based or self-hosted services. In summary, a growing range of collaboration approaches exists, from the insecure-but-accessible Google Docs to end-to-end encrypted or self-hosted tools like Proton and CryptPad, and even to the most secure method of storing and editing files locally and sharing them via Signal. The optimal choice will depend on an organization’s specific threat model and its capacity to manage technical complexities.
If organizers are located in the same geographic region, the question naturally arises: does it make sense to bypass the complexities of digital security and simply meet in person? In many cases, experts told WIRED, the answer is a resounding yes—but with important caveats. Just as with digital organizing, the same threat model evaluation must be applied to in-person meetings. Is the association between the individuals meeting already public knowledge? Or is the fact that they know each other and work together a secret? This same evaluation must extend to the chosen meeting location and any other places they might visit together, mirroring the scrutiny applied to where and how sensitive digital data is stored.
If the very act of being seen together or arriving at/departing from a secret or sensitive location must remain confidential, then meeting in person may not, in fact, offer privacy benefits. Participants could be observed by casual bystanders, followed by law enforcement, or tracked through various physical surveillance methods such as cell phone data triangulation, ubiquitous surveillance cameras, advanced face recognition systems, automatic license plate readers, or any of the myriad ways individuals can be monitored in the physical world.
However, similar to the threat model assessment for data, there are undoubtedly numerous situations where affiliations are already public or non-sensitive. This includes meeting people from one’s own neighborhood, individuals regularly encountered through a religious group, labor union, or any other non-secret organization. In such contexts, where being seen together does not reveal anything sensitive, experts strongly emphasize that in-person meetings remain one of the most valuable and potentially secure ways to collaborate and build solidarity.
"The communication that people have together physically can never be replaced, and I champion it," states Harlo Holmes of the Freedom of the Press Foundation. "I would like to say that the best encryption is the noisy bar where you’re whispering to somebody. But we always do have to think about surveillance architecture, which is incredibly prevalent." In essence, meeting in person eliminates many technical vulnerabilities that could compromise an organization’s privacy and security. However, it’s crucial to consider the threat model: if the very fact of the meeting needs to remain secret, then physical surveillance can render in-person gatherings just as—or even more—risky than digital communications.
The fundamental truth, according to Distribute Aid’s Taylor Fairbank, is that any form of organizing that challenges the interests of powerful entities, whether digital or physical, inherently carries a threat of surveillance and its associated consequences. "There’s always going to be some inherent risk to helping other people, unfortunately," Fairbank acknowledges. "That’s the reality that we live in, so think about what you’re doing. Build your own threat model. And if you’re not willing to accept the inherent risks of doing something, then don’t do it."
However, Fairbank also powerfully asserts that these considerations should not become an insurmountable barrier to action. "Look at the risk in context, make informed choices, try to be as safe as possible," Fairbank urges. "But, my God, go out there and help people. Because we need it." The call to action is clear: understand the risks, equip oneself with the necessary tools and knowledge, and then proceed with informed caution and unwavering commitment to the cause.